# Dynamic Application Security Testing (DAST)
> 原文:[https://docs.gitlab.com/ee/user/application_security/dast/](https://docs.gitlab.com/ee/user/application_security/dast/)
* [Overview](#overview)
* [Use cases](#use-cases)
* [Requirements](#requirements)
* [Configuration](#configuration)
* [When DAST scans run](#when-dast-scans-run)
* [Hide sensitive information](#hide-sensitive-information)
* [Authentication](#authentication)
* [Full scan](#full-scan)
* [Domain validation](#domain-validation)
* [Ruby on Rails](#ruby-on-rails)
* [Django](#django)
* [Node (with Express)](#node-with-express)
* [Domain validation header via a proxy](#domain-validation-header-via-a-proxy)
* [API scan](#api-scan)
* [Specification format](#specification-format)
* [Import API specification from a URL](#import-api-specification-from-a-url)
* [Import API specification from a file](#import-api-specification-from-a-file)
* [Full scan](#full-scan-1)
* [Host override](#host-override)
* [Authentication using headers](#authentication-using-headers)
* [Customizing the DAST settings](#customizing-the-dast-settings)
* [Available variables](#available-variables)
* [DAST command-line options](#dast-command-line-options)
* [Custom ZAProxy configuration](#custom-zaproxy-configuration)
* [Cloning the project’s repository](#cloning-the-projects-repository)
* [Debugging DAST jobs](#debugging-dast-jobs)
* [Running DAST in an offline environment](#running-dast-in-an-offline-environment)
* [Requirements for offline DAST support](#requirements-for-offline-dast-support)
* [Make GitLab DAST analyzer images available inside your Docker registry](#make-gitlab-dast-analyzer-images-available-inside-your-docker-registry)
* [Set DAST CI job variables to use local DAST analyzers](#set-dast-ci-job-variables-to-use-local-dast-analyzers)
* [On-Demand Scans](#on-demand-scans)
* [Enable or disable On-Demand Scans](#enable-or-disable-on-demand-scans)
* [Reports](#reports)
* [List of URLs scanned](#list-of-urls-scanned)
* [JSON](#json)
* [Other formats](#other-formats)
* [Security Dashboard](#security-dashboard)
* [Bleeding-edge vulnerability definitions](#bleeding-edge-vulnerability-definitions)
* [Interacting with the vulnerabilities](#interacting-with-the-vulnerabilities)
* [Vulnerabilities database update](#vulnerabilities-database-update)
* [Optimizing DAST](#optimizing-dast)
* [Troubleshooting](#troubleshooting)
* [Running out of memory](#running-out-of-memory)
# Dynamic Application Security Testing (DAST)[](#dynamic-application-security-testing-dast-ultimate "Permalink")
[Introduced](https://gitlab.com/gitlab-org/gitlab/-/issues/4348) in [GitLab Ultimate](https://about.gitlab.com/pricing/) 10.4.
**注意:**白皮書["應用程序安全性發生](https://about.gitlab.com/resources/whitepaper-seismic-shift-application-security/)了[地震變化"](https://about.gitlab.com/resources/whitepaper-seismic-shift-application-security/)說明**了前 6 種攻擊中有 4 種是基于應用程序的** . 下載它以了解如何保護您的組織.
對代碼運行[靜態檢查](../sast/index.html)是檢測可能使代碼安全性受到威脅的漏洞的第一步. 但是,一旦部署,您的應用程序將面臨一類新的可能的攻擊,例如跨站點腳本或損壞的身份驗證缺陷. 這是動態應用程序安全性測試(DAST)實施的地方.
## Overview[](#overview "Permalink")
如果您使用的是[GitLab CI / CD](../../../ci/README.html) ,則可以使用動態應用程序安全性測試(DAST)分析運行中的 Web 應用程序是否存在已知漏洞. 您可以通過在現有`.gitlab-ci.yml`文件中[包含 CI 作業](#configuration) ,或通過隱式使用[Auto DevOps](../../../topics/autodevops/index.html)提供的[Auto](../../../topics/autodevops/index.html) [DAST](../../../topics/autodevops/stages.html#auto-dast-ultimate)來利用[DAST](../../../topics/autodevops/stages.html#auto-dast-ultimate) .
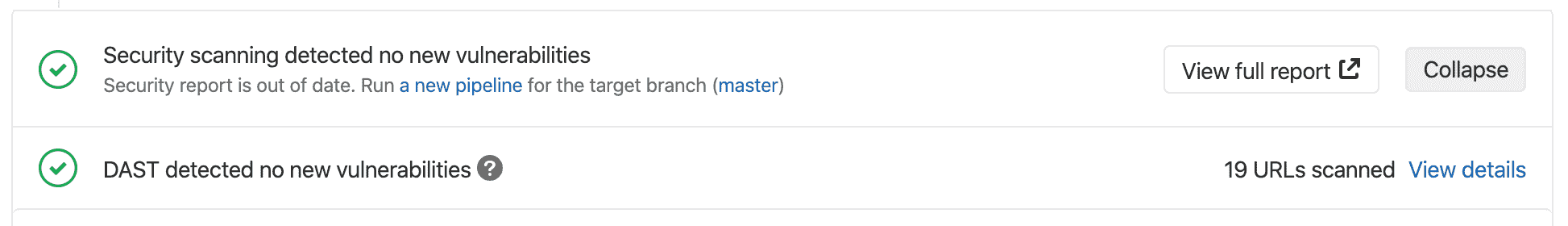
GitLab 檢查 DAST 報告,比較發現的源分支和目標分支之間的漏洞,并顯示有關合并請求的信息.
**注意:**此比較邏輯僅使用針對目標分支的基本提交執行的最新管道. 在任何其他提交上運行管道對合并請求沒有影響.
[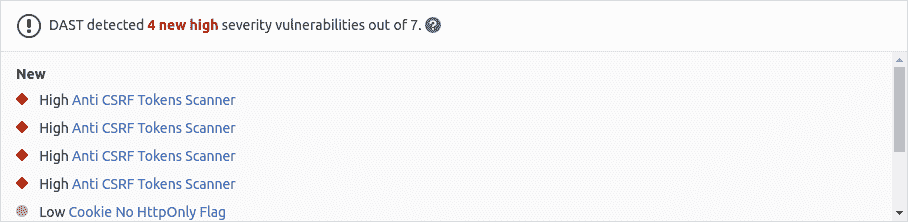](img/dast_v13_2.png)
通過單擊檢測到的鏈接漏洞之一,您可以查看詳細信息和受影響的 URL.
[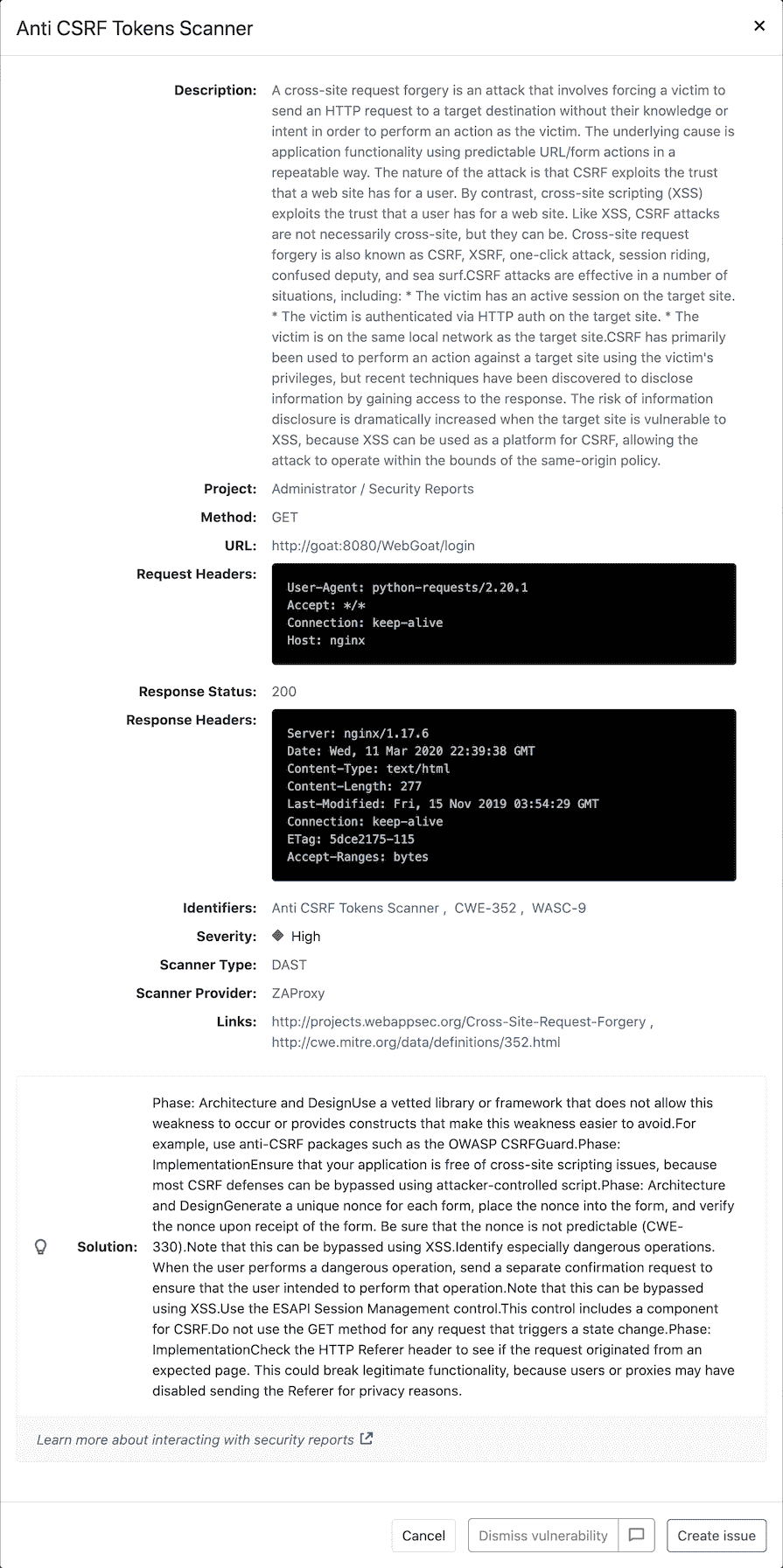](img/dast_single_v13_0.png)
[動態應用程序安全測試(DAST)](https://en.wikipedia.org/wiki/Dynamic_Application_Security_Testing)使用流行的開源工具[OWASP Zed Attack Proxy](https://www.zaproxy.org/)對運行中的 Web 應用程序執行分析.
默認情況下,DAST 執行[ZAP 基準掃描](https://www.zaproxy.org/docs/docker/baseline-scan/)并僅執行被動掃描. 它不會主動攻擊您的應用程序. 但是,可以將 DAST [配置](#full-scan)為還執行*主動掃描* :攻擊您的應用程序并生成更廣泛的安全報告. 與[Review Apps](../../../ci/review_apps/index.html)結合使用可能非常有用.
**注意:**管道可能包含多個作業,包括 SAST 和 DAST 掃描. 如果任何作業由于任何原因未能完成,則安全信息中心將不會顯示 DAST 掃描儀輸出. 例如,如果 DAST 作業完成但 SAST 作業失敗,則安全性儀表板將不會顯示 DAST 結果. 分析器將在失敗時輸出[退出代碼](../../../development/integrations/secure.html#exit-code) .
## Use cases[](#use-cases "Permalink")
它可以幫助您在開發和測試應用程序時自動查找正在運行的 Web 應用程序中的安全漏洞.
## Requirements[](#requirements "Permalink")
要運行 DAST 作業,您需要具有[`docker` executor 的](https://docs.gitlab.com/runner/executors/docker.html) GitLab Runner.
## Configuration[](#configuration "Permalink")
對于 GitLab 11.9 和更高版本,要啟用 DAST,您必須[包含](../../../ci/yaml/README.html#includetemplate) [`DAST.gitlab-ci.yml`模板](https://gitlab.com/gitlab-org/gitlab/blob/master/lib/gitlab/ci/templates/Security/DAST.gitlab-ci.yml) ,該[模板](https://gitlab.com/gitlab-org/gitlab/blob/master/lib/gitlab/ci/templates/Security/DAST.gitlab-ci.yml)作為 GitLab 安裝的一部分提供. 對于 11.9 之前的 GitLab 版本,您可以復制和使用該模板中定義的作業.
將以下內容添加到您的`.gitlab-ci.yml`文件中:
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_WEBSITE: https://example.com
```
有兩種方法來定義要由 DAST 掃描的 URL:
1. 設置`DAST_WEBSITE` [變量](../../../ci/yaml/README.html#variables) .
2. 將其添加到項目根目錄的`environment_url.txt`文件中. 這非常適合在動態環境中進行測試. 為了針對在 GitLab CI / CD 管道中動態創建的應用程序運行 DAST,請讓該應用程序將其域保留在`environment_url.txt`文件中,然后 DAST 自動解析該文件以找到其掃描目標. 您可以在我們的 Auto DevOps CI YAML 中看到一個[示例](https://gitlab.com/gitlab-org/gitlab/blob/master/lib/gitlab/ci/templates/Jobs/Deploy.gitlab-ci.yml) .
如果同時設置了兩個值,則`DAST_WEBSITE`值優先.
隨附的模板會在 CI / CD 管道中創建`dast`工作,并掃描項目的源代碼中可能存在的漏洞.
結果將保存為[DAST 報告工件](../../../ci/pipelines/job_artifacts.html#artifactsreportsdast-ultimate) ,您可以稍后下載和分析. 由于實施限制,我們始終采用最新的 DAST 工件. 在后臺, [GitLab DAST Docker 映像](https://gitlab.com/gitlab-org/security-products/dast)用于在指定的 URL 上運行測試并掃描它是否存在漏洞.
默認情況下,DAST 模板將使用 DAST Docker 映像的最新主版本. 使用`DAST_VERSION`變量,您可以選擇 DAST 更新的方式:
* 通過固定到主要版本(例如`1` )自動更新具有新功能和修復程序的 DAST.
* 僅通過固定到次要版本(例如`1.6` )來更新修補程序.
* 通過固定到特定版本(例如`1.6.4` )來防止所有更新.
在" [發行"](https://gitlab.com/gitlab-org/security-products/dast/-/releases)頁面上找到最新的 DAST 版本.
### When DAST scans run[](#when-dast-scans-run "Permalink")
使用`DAST.gitlab-ci.yml`模板時, `dast`作業最后運行,如下例所示. 為確保 DAST 正在掃描最新代碼,您的 CI 管道應在`dast`作業之前的`dast`作業`dast`更改部署到 Web 服務器.
```
stages:
- build
- test
- deploy
- dast
```
請注意,如果您將管道配置為在每次運行中都部署到同一 Web 服務器,則在另一個管道仍在運行時運行管道可能會導致爭用情況,其中一個管道會覆蓋另一個管道的代碼. 在 DAST 掃描期間,應從更改中排除要掃描的站點. 對該站點的唯一更改應來自 DAST 掃描儀. 請注意,在掃描過程中,用戶,計劃任務,數據庫更改,代碼更改,其他管道或其他掃描程序對站點所做的任何更改都可能導致結果不準確.
### Hide sensitive information[](#hide-sensitive-information "Permalink")
在 GitLab 13.1 中[引入](https://gitlab.com/gitlab-org/gitlab/-/issues/36332) .
HTTP 請求和響應標頭可能包含敏感信息,包括 cookie 和授權憑證. 默認情況下,以下標頭被屏蔽:
* `Authorization`.
* `Proxy-Authorization`.
* `Set-Cookie` (僅值).
* `Cookie` (values only).
使用[`DAST_MASK_HTTP_HEADERS`變量](#available-variables) ,可以列出要屏蔽其值的標頭. 有關如何屏蔽標題的詳細信息,請參閱" [自定義 DAST 設置"](#customizing-the-dast-settings) .
### Authentication[](#authentication "Permalink")
在執行 DAST 檢查之前,還可以對用戶進行身份驗證.
創建掩碼變量以傳遞 DAST 將使用的憑據. 要為用戶名和密碼創建掩碼變量,請參閱[在 UI 中創建自定義變量](../../../ci/variables/README.html#create-a-custom-variable-in-the-ui) . 請注意,username 變量的密鑰必須為`DAST_USERNAME` ,而 password 變量的密鑰必須為`DAST_PASSWORD` .
與認證掃描相關的其他變量是:
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_WEBSITE: https://example.com
DAST_AUTH_URL: https://example.com/sign-in
DAST_USERNAME_FIELD: session[user] # the name of username field at the sign-in HTML form
DAST_PASSWORD_FIELD: session[password] # the name of password field at the sign-in HTML form
DAST_AUTH_EXCLUDE_URLS: http://example.com/sign-out,http://example.com/sign-out-2 # optional, URLs to skip during the authenticated scan; comma-separated, no spaces in between
```
結果將保存為[DAST 報告工件](../../../ci/pipelines/job_artifacts.html#artifactsreportsdast-ultimate) ,您以后可以下載和分析. 由于實施限制,我們始終采用最新的 DAST 工件.
**危險:** **切勿**對生產服務器運行經過身份驗證的掃描. 運行經過身份驗證的掃描時,它可以執行經過身份驗證的用戶可以執行的*任何*功能. 這包括修改和刪除數據,提交表單以及跟隨鏈接之類的操作. 僅對測試服務器運行經過身份驗證的掃描.
### Full scan[](#full-scan "Permalink")
可以將 DAST 配置為執行[ZAP 全面掃描](https://github.com/zaproxy/zaproxy/wiki/ZAP-Full-Scan) ,其中包括針對同一目標網站的被動掃描和主動掃描:
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_FULL_SCAN_ENABLED: "true"
```
#### Domain validation[](#domain-validation "Permalink")
DAST 作業可以在任何地方運行,這意味著您可能會意外擊中實時 Web 服務器并可能損壞它們. 您甚至可以減少生產環境. 因此,您應該使用域驗證.
默認情況下,不需要域驗證. 通過將[環境變量](#available-variables) `DAST_FULL_SCAN_DOMAIN_VALIDATION_REQUIRED`設置為`"true"`可能需要它.
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_FULL_SCAN_ENABLED: "true"
DAST_FULL_SCAN_DOMAIN_VALIDATION_REQUIRED: "true"
```
由于 ZAP 全面掃描會主動攻擊目標應用程序,因此 DAST 會事先向目標(通常在`DAST_WEBSITE`或`environment_url.txt`定義)發送 ping 命令.
* 如果`DAST_FULL_SCAN_DOMAIN_VALIDATION_REQUIRED`為`false`或未設置,則將繼續進行掃描,除非對 ping 的響應包含值為`deny`的`Gitlab-DAST-Permission`標頭.
* 如果`DAST_FULL_SCAN_DOMAIN_VALIDATION_REQUIRED`是`true` ,則掃描將退出除非對 ping 響應包括一個`Gitlab-DAST-Permission`用的頭值`allow` .
以下是在 Rails,Django 和 Node(使用 Express)中向響應添加`Gitlab-DAST-Permission`標頭的一些示例.
##### Ruby on Rails[](#ruby-on-rails "Permalink")
這是[在 Ruby on Rails 中](https://guides.rubyonrails.org/action_controller_overview.html#setting-custom-headers)添加[自定義標頭的方法](https://guides.rubyonrails.org/action_controller_overview.html#setting-custom-headers) :
```
class DastWebsiteTargetController < ActionController::Base
def dast_website_target
response.headers['Gitlab-DAST-Permission'] = 'allow'
head :ok
end
end
```
##### Django[](#django "Permalink")
Here’s how you would add a [custom header in Django](https://docs.djangoproject.com/en/2.2/ref/request-response/#setting-header-fields):
```
class DastWebsiteTargetView(View):
def head(self, *args, **kwargs):
response = HttpResponse()
response['Gitlab-Dast-Permission'] = 'allow'
return response
```
##### Node (with Express)[](#node-with-express "Permalink")
這是[在 Node(使用 Express)中](http://expressjs0com.icopy.site/en/5x/api.html)添加[自定義標頭的方法](http://expressjs0com.icopy.site/en/5x/api.html) :
```
app.get('/dast-website-target', function(req, res) {
res.append('Gitlab-DAST-Permission', 'allow')
res.send('Respond to DAST ping')
})
```
##### Domain validation header via a proxy[](#domain-validation-header-via-a-proxy "Permalink")
也可以通過代理添加`Gitlab-DAST-Permission`標頭.
###### NGINX[](#nginx "Permalink")
以下配置允許 NGINX 充當反向代理并添加`Gitlab-DAST-Permission` [標頭](http://nginx0org.icopy.site/en/docs/http/ngx_http_headers_module.html) :
```
# default.conf
server {
listen 80;
server_name localhost;
location / {
proxy_pass http://test-application;
add_header Gitlab-DAST-Permission allow;
}
}
```
###### Apache[](#apache "Permalink")
Apache 還可以用作[反向代理,](https://httpd.apache.org/docs/2.4/mod/mod_proxy.html)以添加`Gitlab-DAST-Permission` [標頭](https://httpd.apache.org/docs/current/mod/mod_headers.html) .
為此, `httpd.conf`添加到`httpd.conf` :
```
# httpd.conf
LoadModule proxy_module modules/mod_proxy.so
LoadModule proxy_connect_module modules/mod_proxy_connect.so
LoadModule proxy_http_module modules/mod_proxy_http.so
<VirtualHost *:80>
ProxyPass "/" "http://test-application.com/"
ProxyPassReverse "/" "http://test-application.com/"
Header set Gitlab-DAST-Permission "allow"
</VirtualHost>
```
[此代碼段](https://gitlab.com/gitlab-org/security-products/dast/snippets/1894732)包含完整的`httpd.conf`文件,該文件配置為充當遠程代理并添加`Gitlab-DAST-Permission`標頭.
### API scan[](#api-scan "Permalink")
[Introduced](https://gitlab.com/gitlab-org/gitlab/-/issues/10928) in [GitLab Ultimate](https://about.gitlab.com/pricing/) 12.10.
使用 API??規范作為掃描目標是一種為 URL 注入用于掃描 API 的有用方法. API 掃描中的漏洞規則與普通網站掃描中的漏洞規則不同.
#### Specification format[](#specification-format "Permalink")
API 掃描支持 OpenAPI V2 和 OpenAPI V3 規范. 您可以使用`JSON`或`YAML`定義這些規范.
#### Import API specification from a URL[](#import-api-specification-from-a-url "Permalink")
如果可以通過 URL 訪問 API 規范,則可以直接將該 URL 作為目標傳遞. 該規范不必與要測試的 API 托管在同一主機上.
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_API_SPECIFICATION: http://my.api/api-specification.yml
```
#### Import API specification from a file[](#import-api-specification-from-a-file "Permalink")
如果您的存儲庫中有 API 規范,則可以直接提供規范的文件名作為目標. 規范文件應位于`/zap/wrk`目錄中.
```
dast:
script:
- mkdir -p /zap/wrk
- cp api-specification.yml /zap/wrk/api-specification.yml
- /analyze -t $DAST_WEBSITE
variables:
GIT_STRATEGY: fetch
DAST_API_SPECIFICATION: api-specification.yml
```
#### Full scan[](#full-scan-1 "Permalink")
API 掃描支持完全掃描,可以使用`DAST_FULL_SCAN_ENABLED`環境變量來啟用它. 完整的 API 掃描不支持域驗證.
#### Host override[](#host-override "Permalink")
規范通常定義一個主機,其中包含一個域名和一個端口. 引用的主機可能與 API 的審閱實例的主機不同. 這可能導致導入不正確的 URL,或對不正確的主機進行掃描. 使用`DAST_API_HOST_OVERRIDE`環境變量來覆蓋這些值.
例如,對于包含以下內容的 OpenAPI V3 規范:
```
servers:
- url: https://api.host.com
```
如果 API 的測試版本在`https://api-test.host.com`上運行,則可以使用以下 DAST 配置:
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_API_SPECIFICATION: http://api-test.host.com/api-specification.yml
DAST_API_HOST_OVERRIDE: api-test.host.com
```
請注意, `DAST_API_HOST_OVERRIDE`僅適用于 URL 導入的規范.
#### Authentication using headers[](#authentication-using-headers "Permalink")
請求標頭中的令牌通常用作驗證 API 請求的方式. 您可以通過使用`DAST_REQUEST_HEADERS`環境變量來實現. 標頭適用于 DAST 提出的每個請求.
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_API_SPECIFICATION: http://api-test.api.com/api-specification.yml
DAST_REQUEST_HEADERS: "Authorization: Bearer my.token"
```
### Customizing the DAST settings[](#customizing-the-dast-settings "Permalink")
**棄用:**從 GitLab 13.0 開始,不再支持[`only`和`except`](../../../ci/yaml/README.html#onlyexcept-basic)的使用. 覆蓋模板時,必須使用[`rules`](../../../ci/yaml/README.html#rules) .
可以使用`.gitlab-ci.yml`的[`variables`](../../../ci/yaml/README.html#variables)參數通過環境變量更改 DAST 設置. 這些變量記錄在[可用變量中](#available-variables) .
例如:
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_WEBSITE: https://example.com
DAST_SPIDER_MINS: 120
```
因為模板是[在](../../../ci/yaml/README.html#include)管道配置[之前評估](../../../ci/yaml/README.html#include)的,所以最后提到的變量將具有優先權.
### Available variables[](#available-variables "Permalink")
可以使用環境變量[配置](#customizing-the-dast-settings) DAST.
| 環境變量 | Type | Description |
| --- | --- | --- |
| `SECURE_ANALYZERS_PREFIX` | URL | 設置用于下載分析器的 Docker 注冊表基地址. |
| `DAST_WEBSITE` | URL | 要掃描的網站的 URL. 如果省略,則必須指定`DAST_API_SPECIFICATION` . |
| `DAST_API_SPECIFICATION` | 網址或字符串 | 要導入的 API 規范. 該規范可以托管在 URL 或`/zap/wrk`目錄中存在的文件的名稱中. 如果省略,則必須指定`DAST_WEBSITE` . |
| `DAST_AUTH_URL` | URL | 目標網站上包含登錄 HTML 表單的頁面的 URL. `DAST_USERNAME`和`DAST_PASSWORD`將與登錄表單一起提交,以創建經過身份驗證的掃描. API 掃描不支持. |
| `DAST_USERNAME` | string | 網站中要驗證的用戶名. |
| `DAST_PASSWORD` | string | 網站中要驗證的密碼. |
| `DAST_USERNAME_FIELD` | string | 登錄 HTML 表單中的用戶名字段名稱. |
| `DAST_PASSWORD_FIELD` | string | 登錄 HTML 表單中的密碼字段名稱. |
| `DAST_MASK_HTTP_HEADERS` | string | 要屏蔽的請求和響應頭的逗號分隔列表(在 GitLab 13.1 中引入). 必須包含**所有**要屏蔽的標頭. 請參閱[默認情況下被屏蔽的標題列表](#hide-sensitive-information) . |
| `DAST_AUTH_EXCLUDE_URLS` | URLs | 經過身份驗證的掃描期間要跳過的 URL; 以逗號分隔,中間沒有空格. API 掃描不支持. |
| `DAST_FULL_SCAN_ENABLED` | boolean | 設置為`true`可以運行[ZAP 全面掃描](https://github.com/zaproxy/zaproxy/wiki/ZAP-Full-Scan)而不是[ZAP 基線掃描](https://github.com/zaproxy/zaproxy/wiki/ZAP-Baseline-Scan) . 默認值: `false` |
| `DAST_FULL_SCAN_DOMAIN_VALIDATION_REQUIRED` | boolean | 設置為`true`以在運行 DAST 全面掃描時要求[域驗證](#domain-validation) . API 掃描不支持. 默認值: `false` |
| `DAST_AUTO_UPDATE_ADDONS` | boolean | ZAP 附件固定在 DAST Docker 映像中的特定版本. 設置為`true`以在掃描開始時下載最新版本. 默認值: `false` |
| `DAST_API_HOST_OVERRIDE` | string | 用于覆蓋 API 規范文件中定義的域. 范例: `example.com:8080` : `example.com:8080` |
| `DAST_EXCLUDE_RULES` | string | 設置為以逗號分隔的漏洞規則 ID 列表,以將其排除在掃描過程之外. 規則 ID 是數字,可以從 DAST 日志或[ZAP 項目中找到](https://github.com/zaproxy/zaproxy/blob/develop/docs/scanners.md) . 例如, `HTTP Parameter Override`的規則 ID 為`10026` . **注意:**在早期版本的 GitLab 中,已執行排除的規則,但禁止生成它們的警報. 在 GitLab 12.10 中[引入](https://gitlab.com/gitlab-org/gitlab/-/issues/118641) . |
| `DAST_REQUEST_HEADERS` | string | 設置為請求標題名稱和值的逗號分隔列表. 標頭將添加到 DAST 提出的每個請求中. 例如, `Cache-control: no-cache,User-Agent: DAST/1.0` |
| `DAST_DEBUG` | boolean | 啟用調試消息輸出. 默認值: `false` |
| `DAST_SPIDER_MINS` | number | 蜘蛛掃描的最大持續時間(以分鐘為單位). 設置為`0`表示無限制. 默認值:一分鐘,如果掃描為完全掃描,則為無限. |
| `DAST_HTML_REPORT` | string | 掃描結束時編寫的 HTML 報告的文件名. |
| `DAST_MARKDOWN_REPORT` | string | 掃描結束時寫入的 Markdown 報告的文件名. |
| `DAST_XML_REPORT` | string | 掃描結束時寫入的 XML 報告的文件名. |
| `DAST_INCLUDE_ALPHA_VULNERABILITIES` | boolean | 設置為`true`以包括 alpha 被動和主動掃描規則. 默認值: `false` |
| `DAST_USE_AJAX_SPIDER` | boolean | 設置為`true`可以除傳統蜘蛛外還使用 AJAX 蜘蛛,對爬網需要 JavaScript 的站點很有用. 默認值: `false` |
| `DAST_ZAP_CLI_OPTIONS` | string | ZAP 服務器命令行選項. 例如, `-Xmx3072m`將設置 Java 最大內存分配池大小. |
| `DAST_ZAP_LOG_CONFIGURATION` | string | 設置為 ZAP 服務器的其他 log4j 屬性的分號分隔列表. 例如, `log4j.logger.org.parosproxy.paros.network.HttpSender=DEBUG;log4j.logger.com.crawljax=DEBUG` |
### DAST command-line options[](#dast-command-line-options "Permalink")
并非所有 DAST 配置都可以通過環境變量獲得. 要找出所有可能的選項,請運行以下配置. 可用的命令行選項將被打印到作業日志中:
```
include:
template: DAST.gitlab-ci.yml
dast:
script:
- /analyze --help
```
然后,您必須覆蓋`script`命令以傳遞適當的參數. 例如,可以使用選項`-D`延遲被動掃描. 以下配置將被動掃描延遲了五分鐘:
```
include:
template: DAST.gitlab-ci.yml
dast:
script:
- export DAST_WEBSITE=${DAST_WEBSITE:-$(cat environment_url.txt)}
- /analyze -D 300 -t $DAST_WEBSITE
```
### Custom ZAProxy configuration[](#custom-zaproxy-configuration "Permalink")
ZAProxy 服務器包含許多[有用的可配置值](https://gitlab.com/gitlab-org/gitlab/-/issues/36437#note_245801885) . `-config`許多鍵/值仍未記錄,但是有未測試的[可能鍵](https://gitlab.com/gitlab-org/gitlab/-/issues/36437#note_244981023)列表. 請注意,DAST 不支持這些選項,并且在使用時可能會中斷 DAST 掃描. 下面是一個如何使用`TOKEN`重寫 Authorization 標頭值的示例:
```
include:
template: DAST.gitlab-ci.yml
variables:
DAST_ZAP_CLI_OPTIONS: "-config replacer.full_list(0).description=auth -config replacer.full_list(0).enabled=true -config replacer.full_list(0).matchtype=REQ_HEADER -config replacer.full_list(0).matchstr=Authorization -config replacer.full_list(0).regex=false -config replacer.full_list(0).replacement=TOKEN"
```
### Cloning the project’s repository[](#cloning-the-projects-repository "Permalink")
DAST 作業在運行時不需要存在項目的存儲庫,因此默認情況下[`GIT_STRATEGY`](../../../ci/yaml/README.html#git-strategy)設置為`none` .
### Debugging DAST jobs[](#debugging-dast-jobs "Permalink")
A DAST job has two executing processes:
* ZAP 服務器.
* 啟動,控制和停止 ZAP 服務器的一系列腳本.
可以使用`DAST_DEBUG`環境變量來啟用腳本的調試模式. 這在對作業進行故障排除時會有所幫助,并且將輸出指示掃描完成百分比的語句. 有關使用變量的詳細信息,請參見[覆蓋 DAST 模板](#customizing-the-dast-settings) .
可以使用`DAST_ZAP_LOG_CONFIGURATION`環境變量啟用 ZAP 服務器的調試模式. 下表概述了可以設置的值的示例,以及它們對記錄的輸出的影響. 可以指定多個值,以分號分隔.
| 日志配置值 | Effect |
| --- | --- |
| `log4j.rootLogger=DEBUG` | 啟用所有調試日志記錄語句. |
| `log4j.logger.org.apache.commons.httpclient=DEBUG` | 記錄 ZAP 服務器所做的每個 HTTP 請求和響應. |
| `log4j.logger.org.zaproxy.zap.spider.SpiderController=DEBUG` | 在目標的蜘蛛掃描期間找到的日志 URL. |
| `log4j.logger.com.crawljax=DEBUG` | 啟用 Ajax Crawler 調試日志記錄語句. |
| `log4j.logger.org.parosproxy.paros=DEBUG` | 啟用 ZAP 服務器代理調試日志記錄語句. |
| `log4j.logger.org.zaproxy.zap=DEBUG` | 啟用常規 ZAP 服務器代碼的調試日志記錄語句. |
## Running DAST in an offline environment[](#running-dast-in-an-offline-environment "Permalink")
對于在通過互聯網有限,受限或間歇性訪問外部資源的環境中進行自我管理的 GitLab 實例,需要進行一些調整才能成功運行 DAST 作業. 有關更多信息,請參閱[脫機環境](../offline_deployments/index.html) .
### Requirements for offline DAST support[](#requirements-for-offline-dast-support "Permalink")
要在離線環境中使用 DAST,您需要:
* GitLab 亞軍與[`docker`或`kubernetes`執行](#requirements) .
* 帶有 DAST [容器映像](https://gitlab.com/gitlab-org/security-products/dast)的本地可用副本的 Docker 容器注冊表,可在[DAST 容器注冊表中找到](https://gitlab.com/gitlab-org/security-products/dast/container_registry) .
**Note:** GitLab Runner has a [default `pull policy` of `always`](https://docs.gitlab.com/runner/executors/docker.html), meaning the Runner tries to pull Docker images from the GitLab container registry even if a local copy is available. GitLab Runner’s [`pull_policy` can be set to `if-not-present`](https://docs.gitlab.com/runner/executors/docker.html) in an offline environment if you prefer using only locally available Docker images. However, we recommend keeping the pull policy setting to `always` if not in an offline environment, as this enables the use of updated scanners in your CI/CD pipelines.
### Make GitLab DAST analyzer images available inside your Docker registry[](#make-gitlab-dast-analyzer-images-available-inside-your-docker-registry "Permalink")
對于 DAST,將以下默認 DAST 分析器映像從`registry.gitlab.com`導入到[本地 Docker 容器注冊表](../../packages/container_registry/index.html) :
* `registry.gitlab.com/gitlab-org/security-products/dast:latest`
The process for importing Docker images into a local offline Docker registry depends on **您的網絡安全政策**. Please consult your IT staff to find an accepted and approved process by which external resources can be imported or temporarily accessed. Note that these scanners are [updated periodically](../index.html#maintenance-and-update-of-the-vulnerabilities-database) with new definitions, so consider if you’re able to make periodic updates yourself.
有關將 Docker 映像保存和傳輸為文件的詳細信息,請參閱 Docker 有關[`docker save`](https://s0docs0docker0com.icopy.site/engine/reference/commandline/save/) , [`docker load`](https://s0docs0docker0com.icopy.site/engine/reference/commandline/load/) , [`docker export`](https://s0docs0docker0com.icopy.site/engine/reference/commandline/export/)和[`docker import`](https://s0docs0docker0com.icopy.site/engine/reference/commandline/import/)的文檔.
### Set DAST CI job variables to use local DAST analyzers[](#set-dast-ci-job-variables-to-use-local-dast-analyzers "Permalink")
將以下配置添加到您的`.gitlab-ci.yml`文件. 您必須替換`image`以引用本地 Docker 容器注冊表中托管的 DAST Docker 映像:
```
include:
- template: DAST.gitlab-ci.yml
dast:
image: registry.example.com/namespace/dast:latest
```
DAST 作業現在應該使用 DAST 分析器的本地副本來掃描您的代碼并生成安全報告,而無需訪問 Internet.
或者,您可以使用變量`SECURE_ANALYZERS_PREFIX`覆蓋`dast`映像的基本注冊表地址.
## On-Demand Scans[](#on-demand-scans "Permalink")
版本歷史
* 在 GitLab 13.2 中[引入](https://gitlab.com/gitlab-org/gitlab/-/issues/218465) .
* 它部署在功能標記后面,默認情況下處于禁用狀態.
* 在 GitLab.com 上已禁用.
* 每個項目都可以啟用或禁用它.
* 要在 GitLab 自管實例中使用它,請讓 GitLab 管理員[啟用它](#enable-or-disable-on-demand-scans) .
在 DevOps 生命周期之外,可以根據需要針對目標網站運行被動 DAST 掃描. 這些掃描將始終與項目的默認分支或`master`分支關聯,并且結果可以在項目儀表板中看到.
[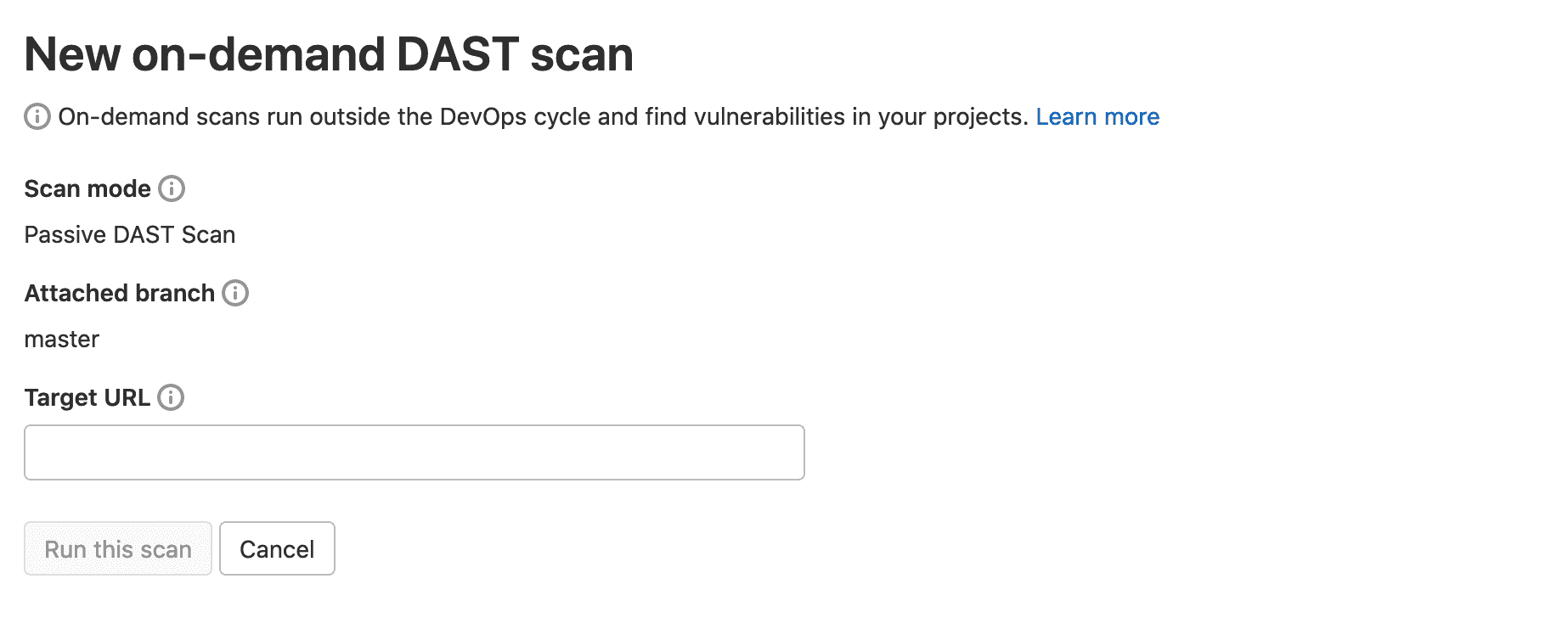](img/dast_on_demand_v13_2.png)
### Enable or disable On-Demand Scans[](#enable-or-disable-on-demand-scans "Permalink")
按需掃描正在開發中,尚未準備好用于生產. 它部署在**默認情況下禁用**的功能標志的后面. [有權訪問 GitLab Rails 控制臺的 GitLab 管理員](../../../administration/feature_flags.html)可以為您的實例啟用它. 可以按項目啟用或禁用按需掃描
要啟用它:
```
# Instance-wide
Feature.enable(:security_on_demand_scans_feature_flag)
# or by project
Feature.enable(:security_on_demand_scans_feature_flag, Project.find(<project id>))
```
To disable it:
```
# Instance-wide
Feature.disable(:security_on_demand_scans_feature_flag)
# or by project
Feature.disable(:security_on_demand_scans_feature_flag, Project.find(<project id>))
```
## Reports[](#reports "Permalink")
默認情況下,DAST 工具以 JSON 格式輸出報告文件. 但是,此工具還可以生成 Markdown,HTML 和 XML 的報告. 有關更多信息,請參閱[DAST 報告](https://gitlab.com/gitlab-org/security-products/security-report-schemas/-/blob/master/dist/dast-report-format.json)的[架構](https://gitlab.com/gitlab-org/security-products/security-report-schemas/-/blob/master/dist/dast-report-format.json) .
### List of URLs scanned[](#list-of-urls-scanned "Permalink")
當 DAST 完成掃描時,合并請求頁面將說明掃描的 URL 數量. 單擊**查看詳細信息**以查看 Web 控制臺輸出,其中包括掃描的 URL 列表.
[](img/dast_urls_scanned_v12_10.png)
### JSON[](#json "Permalink")
**警告:** JSON 報表工件不是 DAST 的公共 API,并且其格式預計會在將來更改.
DAST 工具始終會發出一個名為`gl-dast-report.json`的 JSON 報告文件,并且可以在[DAST 存儲庫中](https://gitlab.com/gitlab-org/security-products/dast/-/tree/master/test/end-to-end/expect)找到示例報告.
JSON 報表中有兩種數據格式可以并排使用:
* 專有的 ZAP 格式將最終棄用.
* 一種通用格式,將來會成為默認格式.
### Other formats[](#other-formats "Permalink")
還可以用 Markdown,HTML 和 XML 生成報告. 這些可以使用以下配置作為工件發布:
```
include:
template: DAST.gitlab-ci.yml
dast:
variables:
DAST_HTML_REPORT: report.html
DAST_MARKDOWN_REPORT: report.md
DAST_XML_REPORT: report.xml
artifacts:
paths:
- $DAST_HTML_REPORT
- $DAST_MARKDOWN_REPORT
- $DAST_XML_REPORT
- gl-dast-report.json
```
## Security Dashboard[](#security-dashboard "Permalink")
在"安全儀表板"中,您可以概覽您的組,項目和管道中的所有安全漏洞. 閱讀有關[安全儀表板的](../security_dashboard/index.html)更多[信息](../security_dashboard/index.html) .
## Bleeding-edge vulnerability definitions[](#bleeding-edge-vulnerability-definitions "Permalink")
ZAP 首先在`alpha`類中創建規則. 經過與社區的測試期后,他們被提升為`beta` . 默認情況下,DAST 使用`beta`定義. 要請求`alpha`定義,請使用`DAST_INCLUDE_ALPHA_VULNERABILITIES`環境變量,如以下配置所示:
```
include:
template: DAST.gitlab-ci.yml
variables:
DAST_INCLUDE_ALPHA_VULNERABILITIES: true
```
## Interacting with the vulnerabilities[](#interacting-with-the-vulnerabilities "Permalink")
一旦發現漏洞,便可以與其進行交互. 閱讀有關如何[與漏洞](../index.html#interacting-with-the-vulnerabilities)進行[交互的](../index.html#interacting-with-the-vulnerabilities)更多信息.
## Vulnerabilities database update[](#vulnerabilities-database-update "Permalink")
有關漏洞數據庫更新的更多信息,請查看[維護表](../index.html#maintenance-and-update-of-the-vulnerabilities-database) .
## Optimizing DAST[](#optimizing-dast "Permalink")
默認情況下,DAST 將下載管道中先前作業定義的所有工件. 如果您的 DAST 作業不依賴`environment_url.txt`來定義被測 URL 或以前的作業中創建的任何其他文件,我們建議您不要下載工件. 為了避免下載工件,請將以下內容添加到您的`gitlab-ci.yml`文件中:
```
dast: dependencies: []
```
## Troubleshooting[](#troubleshooting "Permalink")
### Running out of memory[](#running-out-of-memory "Permalink")
默認情況下,DAST 依賴的 ZAProxy 被分配的內存總計為主機上總內存的 25%. 由于它在掃描期間將大部分信息保留在內存中,因此 DAST 在掃描大型應用程序時可能會用盡內存. 這將導致以下錯誤:
```
[zap.out] java.lang.OutOfMemoryError: Java heap space
```
幸運的是,通過使用`DAST_ZAP_CLI_OPTIONS`環境變量可以直接增加 DAST 可用的內存量:
```
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_ZAP_CLI_OPTIONS: "-Xmx3072m"
```
在此,DAST 被分配了 3072 MB. 將`-Xmx`之后的數字更改為所需的存儲量.
- GitLab Docs
- Installation
- Requirements
- GitLab cloud native Helm Chart
- Install GitLab with Docker
- Installation from source
- Install GitLab on Microsoft Azure
- Installing GitLab on Google Cloud Platform
- Installing GitLab on Amazon Web Services (AWS)
- Analytics
- Code Review Analytics
- Productivity Analytics
- Value Stream Analytics
- Kubernetes clusters
- Adding and removing Kubernetes clusters
- Adding EKS clusters
- Adding GKE clusters
- Group-level Kubernetes clusters
- Instance-level Kubernetes clusters
- Canary Deployments
- Cluster Environments
- Deploy Boards
- GitLab Managed Apps
- Crossplane configuration
- Cluster management project (alpha)
- Kubernetes Logs
- Runbooks
- Serverless
- Deploying AWS Lambda function using GitLab CI/CD
- Securing your deployed applications
- Groups
- Contribution Analytics
- Custom group-level project templates
- Epics
- Manage epics
- Group Import/Export
- Insights
- Issues Analytics
- Iterations
- Public access
- SAML SSO for GitLab.com groups
- SCIM provisioning using SAML SSO for GitLab.com groups
- Subgroups
- Roadmap
- Projects
- GitLab Secure
- Security Configuration
- Container Scanning
- Dependency Scanning
- Dependency List
- Static Application Security Testing (SAST)
- Secret Detection
- Dynamic Application Security Testing (DAST)
- GitLab Security Dashboard
- Offline environments
- Standalone Vulnerability pages
- Security scanner integration
- Badges
- Bulk editing issues and merge requests at the project level
- Code Owners
- Compliance
- License Compliance
- Compliance Dashboard
- Create a project
- Description templates
- Deploy Keys
- Deploy Tokens
- File finder
- Project integrations
- Integrations
- Atlassian Bamboo CI Service
- Bugzilla Service
- Custom Issue Tracker service
- Discord Notifications service
- Enabling emails on push
- GitHub project integration
- Hangouts Chat service
- Atlassian HipChat
- Irker IRC Gateway
- GitLab Jira integration
- Mattermost Notifications Service
- Mattermost slash commands
- Microsoft Teams service
- Mock CI Service
- Prometheus integration
- Redmine Service
- Slack Notifications Service
- Slack slash commands
- GitLab Slack application
- Webhooks
- YouTrack Service
- Insights
- Issues
- Crosslinking Issues
- Design Management
- Confidential issues
- Due dates
- Issue Boards
- Issue Data and Actions
- Labels
- Managing issues
- Milestones
- Multiple Assignees for Issues
- Related issues
- Service Desk
- Sorting and ordering issue lists
- Issue weight
- Associate a Zoom meeting with an issue
- Merge requests
- Allow collaboration on merge requests across forks
- Merge Request Approvals
- Browser Performance Testing
- How to create a merge request
- Cherry-pick changes
- Code Quality
- Load Performance Testing
- Merge Request dependencies
- Fast-forward merge requests
- Merge when pipeline succeeds
- Merge request conflict resolution
- Reverting changes
- Reviewing and managing merge requests
- Squash and merge
- Merge requests versions
- Draft merge requests
- Members of a project
- Migrating projects to a GitLab instance
- Import your project from Bitbucket Cloud to GitLab
- Import your project from Bitbucket Server to GitLab
- Migrating from ClearCase
- Migrating from CVS
- Import your project from FogBugz to GitLab
- Gemnasium
- Import your project from GitHub to GitLab
- Project importing from GitLab.com to your private GitLab instance
- Import your project from Gitea to GitLab
- Import your Jira project issues to GitLab
- Migrating from Perforce Helix
- Import Phabricator tasks into a GitLab project
- Import multiple repositories by uploading a manifest file
- Import project from repo by URL
- Migrating from SVN to GitLab
- Migrating from TFVC to Git
- Push Options
- Releases
- Repository
- Branches
- Git Attributes
- File Locking
- Git file blame
- Git file history
- Repository mirroring
- Protected branches
- Protected tags
- Push Rules
- Reduce repository size
- Signing commits with GPG
- Syntax Highlighting
- GitLab Web Editor
- Web IDE
- Requirements Management
- Project settings
- Project import/export
- Project access tokens (Alpha)
- Share Projects with other Groups
- Snippets
- Static Site Editor
- Wiki
- Project operations
- Monitor metrics for your CI/CD environment
- Set up alerts for Prometheus metrics
- Embedding metric charts within GitLab-flavored Markdown
- Embedding Grafana charts
- Using the Metrics Dashboard
- Dashboard YAML properties
- Metrics dashboard settings
- Panel types for dashboards
- Using Variables
- Templating variables for metrics dashboards
- Prometheus Metrics library
- Monitoring AWS Resources
- Monitoring HAProxy
- Monitoring Kubernetes
- Monitoring NGINX
- Monitoring NGINX Ingress Controller
- Monitoring NGINX Ingress Controller with VTS metrics
- Alert Management
- Error Tracking
- Tracing
- Incident Management
- GitLab Status Page
- Feature Flags
- GitLab CI/CD
- GitLab CI/CD pipeline configuration reference
- GitLab CI/CD include examples
- Introduction to CI/CD with GitLab
- Getting started with GitLab CI/CD
- How to enable or disable GitLab CI/CD
- Using SSH keys with GitLab CI/CD
- Migrating from CircleCI
- Migrating from Jenkins
- Auto DevOps
- Getting started with Auto DevOps
- Requirements for Auto DevOps
- Customizing Auto DevOps
- Stages of Auto DevOps
- Upgrading PostgreSQL for Auto DevOps
- Cache dependencies in GitLab CI/CD
- GitLab ChatOps
- Cloud deployment
- Docker integration
- Building Docker images with GitLab CI/CD
- Using Docker images
- Building images with kaniko and GitLab CI/CD
- GitLab CI/CD environment variables
- Predefined environment variables reference
- Where variables can be used
- Deprecated GitLab CI/CD variables
- Environments and deployments
- Protected Environments
- GitLab CI/CD Examples
- Test a Clojure application with GitLab CI/CD
- Using Dpl as deployment tool
- Testing a Phoenix application with GitLab CI/CD
- End-to-end testing with GitLab CI/CD and WebdriverIO
- DevOps and Game Dev with GitLab CI/CD
- Deploy a Spring Boot application to Cloud Foundry with GitLab CI/CD
- How to deploy Maven projects to Artifactory with GitLab CI/CD
- Testing PHP projects
- Running Composer and NPM scripts with deployment via SCP in GitLab CI/CD
- Test and deploy Laravel applications with GitLab CI/CD and Envoy
- Test and deploy a Python application with GitLab CI/CD
- Test and deploy a Ruby application with GitLab CI/CD
- Test and deploy a Scala application to Heroku
- GitLab CI/CD for external repositories
- Using GitLab CI/CD with a Bitbucket Cloud repository
- Using GitLab CI/CD with a GitHub repository
- GitLab Pages
- GitLab Pages
- GitLab Pages domain names, URLs, and baseurls
- Create a GitLab Pages website from scratch
- Custom domains and SSL/TLS Certificates
- GitLab Pages integration with Let's Encrypt
- GitLab Pages Access Control
- Exploring GitLab Pages
- Incremental Rollouts with GitLab CI/CD
- Interactive Web Terminals
- Optimizing GitLab for large repositories
- Metrics Reports
- CI/CD pipelines
- Pipeline Architecture
- Directed Acyclic Graph
- Multi-project pipelines
- Parent-child pipelines
- Pipelines for Merge Requests
- Pipelines for Merged Results
- Merge Trains
- Job artifacts
- Pipeline schedules
- Pipeline settings
- Triggering pipelines through the API
- Review Apps
- Configuring GitLab Runners
- GitLab CI services examples
- Using MySQL
- Using PostgreSQL
- Using Redis
- Troubleshooting CI/CD
- GitLab Package Registry
- GitLab Container Registry
- Dependency Proxy
- GitLab Composer Repository
- GitLab Conan Repository
- GitLab Maven Repository
- GitLab NPM Registry
- GitLab NuGet Repository
- GitLab PyPi Repository
- API Docs
- API resources
- .gitignore API
- GitLab CI YMLs API
- Group and project access requests API
- Appearance API
- Applications API
- Audit Events API
- Avatar API
- Award Emoji API
- Project badges API
- Group badges API
- Branches API
- Broadcast Messages API
- Project clusters API
- Group clusters API
- Instance clusters API
- Commits API
- Container Registry API
- Custom Attributes API
- Dashboard annotations API
- Dependencies API
- Deploy Keys API
- Deployments API
- Discussions API
- Dockerfiles API
- Environments API
- Epics API
- Events
- Feature Flags API
- Feature flag user lists API
- Freeze Periods API
- Geo Nodes API
- Group Activity Analytics API
- Groups API
- Import API
- Issue Boards API
- Group Issue Boards API
- Issues API
- Epic Issues API
- Issues Statistics API
- Jobs API
- Keys API
- Labels API
- Group Labels API
- License
- Licenses API
- Issue links API
- Epic Links API
- Managed Licenses API
- Markdown API
- Group and project members API
- Merge request approvals API
- Merge requests API
- Project milestones API
- Group milestones API
- Namespaces API
- Notes API
- Notification settings API
- Packages API
- Pages domains API
- Pipeline schedules API
- Pipeline triggers API
- Pipelines API
- Project Aliases API
- Project import/export API
- Project repository storage moves API
- Project statistics API
- Project templates API
- Projects API
- Protected branches API
- Protected tags API
- Releases API
- Release links API
- Repositories API
- Repository files API
- Repository submodules API
- Resource label events API
- Resource milestone events API
- Resource weight events API
- Runners API
- SCIM API
- Search API
- Services API
- Application settings API
- Sidekiq Metrics API
- Snippets API
- Project snippets
- Application statistics API
- Suggest Changes API
- System hooks API
- Tags API
- Todos API
- Users API
- Project-level Variables API
- Group-level Variables API
- Version API
- Vulnerabilities API
- Vulnerability Findings API
- Wikis API
- GraphQL API
- Getting started with GitLab GraphQL API
- GraphQL API Resources
- API V3 to API V4
- Validate the .gitlab-ci.yml (API)
- User Docs
- Abuse reports
- User account
- Active sessions
- Deleting a User account
- Permissions
- Personal access tokens
- Profile preferences
- Threads
- GitLab and SSH keys
- GitLab integrations
- Git
- GitLab.com settings
- Infrastructure as code with Terraform and GitLab
- GitLab keyboard shortcuts
- GitLab Markdown
- AsciiDoc
- GitLab Notification Emails
- GitLab Quick Actions
- Autocomplete characters
- Reserved project and group names
- Search through GitLab
- Advanced Global Search
- Advanced Syntax Search
- Time Tracking
- GitLab To-Do List
- Administrator Docs
- Reference architectures
- Reference architecture: up to 1,000 users
- Reference architecture: up to 2,000 users
- Reference architecture: up to 3,000 users
- Reference architecture: up to 5,000 users
- Reference architecture: up to 10,000 users
- Reference architecture: up to 25,000 users
- Reference architecture: up to 50,000 users
- Troubleshooting a reference architecture set up
- Working with the bundled Consul service
- Configuring PostgreSQL for scaling
- Configuring GitLab application (Rails)
- Load Balancer for multi-node GitLab
- Configuring a Monitoring node for Scaling and High Availability
- NFS
- Working with the bundled PgBouncer service
- Configuring Redis for scaling
- Configuring Sidekiq
- Admin Area settings
- Continuous Integration and Deployment Admin settings
- Custom instance-level project templates
- Diff limits administration
- Enable and disable GitLab features deployed behind feature flags
- Geo nodes Admin Area
- GitLab Pages administration
- Health Check
- Job logs
- Labels administration
- Log system
- PlantUML & GitLab
- Repository checks
- Repository storage paths
- Repository storage types
- Account and limit settings
- Service templates
- System hooks
- Changing your time zone
- Uploads administration
- Abuse reports
- Activating and deactivating users
- Audit Events
- Blocking and unblocking users
- Broadcast Messages
- Elasticsearch integration
- Gitaly
- Gitaly Cluster
- Gitaly reference
- Monitoring GitLab
- Monitoring GitLab with Prometheus
- Performance Bar
- Usage statistics
- Object Storage
- Performing Operations in GitLab
- Cleaning up stale Redis sessions
- Fast lookup of authorized SSH keys in the database
- Filesystem Performance Benchmarking
- Moving repositories managed by GitLab
- Run multiple Sidekiq processes
- Sidekiq MemoryKiller
- Switching to Puma
- Understanding Unicorn and unicorn-worker-killer
- User lookup via OpenSSH's AuthorizedPrincipalsCommand
- GitLab Package Registry administration
- GitLab Container Registry administration
- Replication (Geo)
- Geo database replication
- Geo with external PostgreSQL instances
- Geo configuration
- Using a Geo Server
- Updating the Geo nodes
- Geo with Object storage
- Docker Registry for a secondary node
- Geo for multiple nodes
- Geo security review (Q&A)
- Location-aware Git remote URL with AWS Route53
- Tuning Geo
- Removing secondary Geo nodes
- Geo data types support
- Geo Frequently Asked Questions
- Geo Troubleshooting
- Geo validation tests
- Disaster Recovery (Geo)
- Disaster recovery for planned failover
- Bring a demoted primary node back online
- Automatic background verification
- Rake tasks
- Back up and restore GitLab
- Clean up
- Namespaces
- Maintenance Rake tasks
- Geo Rake Tasks
- GitHub import
- Import bare repositories
- Integrity check Rake task
- LDAP Rake tasks
- Listing repository directories
- Praefect Rake tasks
- Project import/export administration
- Repository storage Rake tasks
- Generate sample Prometheus data
- Uploads migrate Rake tasks
- Uploads sanitize Rake tasks
- User management
- Webhooks administration
- X.509 signatures
- Server hooks
- Static objects external storage
- Updating GitLab
- GitLab release and maintenance policy
- Security
- Password Storage
- Custom password length limits
- Restrict allowed SSH key technologies and minimum length
- Rate limits
- Webhooks and insecure internal web services
- Information exclusivity
- How to reset your root password
- How to unlock a locked user from the command line
- User File Uploads
- How we manage the TLS protocol CRIME vulnerability
- User email confirmation at sign-up
- Security of running jobs
- Proxying assets
- CI/CD Environment Variables
- Contributor and Development Docs
- Contribute to GitLab
- Community members & roles
- Implement design & UI elements
- Issues workflow
- Merge requests workflow
- Code Review Guidelines
- Style guides
- GitLab Architecture Overview
- CI/CD development documentation
- Database guides
- Database Review Guidelines
- Database Review Guidelines
- Migration Style Guide
- What requires downtime?
- Understanding EXPLAIN plans
- Rake tasks for developers
- Mass inserting Rails models
- GitLab Documentation guidelines
- Documentation Style Guide
- Documentation structure and template
- Documentation process
- Documentation site architecture
- Global navigation
- GitLab Docs monthly release process
- Telemetry Guide
- Usage Ping Guide
- Snowplow Guide
- Experiment Guide
- Feature flags in development of GitLab
- Feature flags process
- Developing with feature flags
- Feature flag controls
- Document features deployed behind feature flags
- Frontend Development Guidelines
- Accessibility & Readability
- Ajax
- Architecture
- Axios
- Design Patterns
- Frontend Development Process
- DropLab
- Emojis
- Filter
- Frontend FAQ
- GraphQL
- Icons and SVG Illustrations
- InputSetter
- Performance
- Principles
- Security
- Tooling
- Vuex
- Vue
- Geo (development)
- Geo self-service framework (alpha)
- Gitaly developers guide
- GitLab development style guides
- API style guide
- Go standards and style guidelines
- GraphQL API style guide
- Guidelines for shell commands in the GitLab codebase
- HTML style guide
- JavaScript style guide
- Migration Style Guide
- Newlines style guide
- Python Development Guidelines
- SCSS style guide
- Shell scripting standards and style guidelines
- Sidekiq debugging
- Sidekiq Style Guide
- SQL Query Guidelines
- Vue.js style guide
- Instrumenting Ruby code
- Testing standards and style guidelines
- Flaky tests
- Frontend testing standards and style guidelines
- GitLab tests in the Continuous Integration (CI) context
- Review Apps
- Smoke Tests
- Testing best practices
- Testing levels
- Testing Rails migrations at GitLab
- Testing Rake tasks
- End-to-end Testing
- Beginner's guide to writing end-to-end tests
- End-to-end testing Best Practices
- Dynamic Element Validation
- Flows in GitLab QA
- Page objects in GitLab QA
- Resource class in GitLab QA
- Style guide for writing end-to-end tests
- Testing with feature flags
- Translate GitLab to your language
- Internationalization for GitLab
- Translating GitLab
- Proofread Translations
- Merging translations from CrowdIn
- Value Stream Analytics development guide
- GitLab subscription
- Activate GitLab EE with a license